Apple sent security alerts to people in 92 countries on Wednesday, warning that their iPhones had been remotely targeted in a mercenary spyware attack.
“Apple detected that you are being targeted by a mercenary spyware attack,” the company said in a threat notification email seen by many. “This attack is likely targeting you specifically because of who you are or what you do.”
Mercenary attacks, compared to cybercrimes or consumer malware, stand out due to their rarity and complexity. These meticulously orchestrated attacks cost millions of dollars and focus on a small number of people. The targeting is ongoing and global, the company said in the email.
“If your device is compromised by a targeted mercenary spyware attack, the attacker may be able to remotely access your sensitive data, communications, or even the camera and microphone,” the threat notification email said.
A mercenary spyware attack on an Apple iPhone typically involves the use of sophisticated malware developed and deployed by private companies or individuals for the purpose of surveillance. This spyware can infiltrate the iPhone through various means, such as malicious links, fake apps, or exploiting vulnerabilities in the iOS operating system. Once installed, the spyware can monitor and record various activities on the device, including calls, messages, emails, browsing history, and even location data.
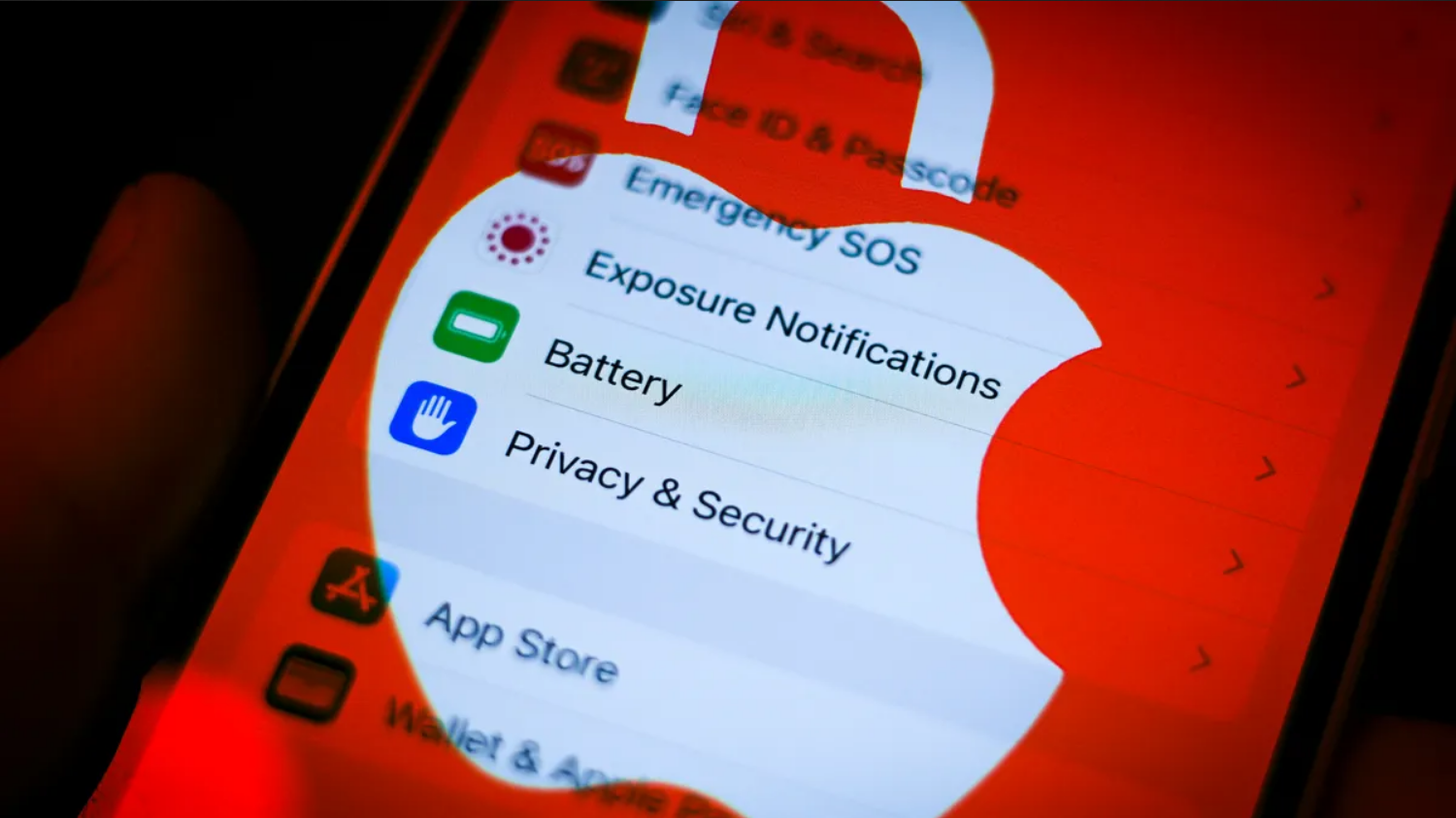
To prevent and protect themselves from such attacks, iPhone users can take several measures:
- Keep the iOS software updated: Apple regularly releases updates to patch security vulnerabilities and improve the overall security of the operating system. Users should ensure that their iPhones are running the latest version of iOS to mitigate the risk of exploitation by spyware.
- Avoid clicking on suspicious links: Spyware can often be installed through phishing attacks, where users are tricked into clicking on malicious links or downloading infected files. Users should exercise caution when clicking on links from unknown or untrusted sources, especially in emails, messages, or social media.
- Download apps only from the App Store: Apple has stringent security measures in place to vet and approve apps before they are made available on the App Store. Users should refrain from downloading apps from third-party sources, as these may contain malware or spyware. Additionally, they should review the permissions requested by apps before installing them and avoid granting unnecessary access to sensitive data.
- Enable two-factor authentication: Two-factor authentication adds an extra layer of security to Apple ID accounts, making it more difficult for unauthorized individuals to access users’ data and devices. Users should enable two-factor authentication for their Apple ID and ensure that their devices are linked to trusted phone numbers or email addresses for verification.
- Regularly review device settings and permissions: Users should periodically review the privacy and security settings on their iPhones to ensure that only necessary permissions are granted to apps and services. This includes reviewing which apps have access to location data, camera, microphone, contacts, and other sensitive information, and revoking permissions for any apps that do not require them.
- Use strong, unique passwords: Strong, unique passwords are essential for protecting Apple ID accounts and preventing unauthorized access to devices and data. Users should create complex passwords that combine letters, numbers, and special characters, and avoid using the same password for multiple accounts.
- Install reputable security software: While iOS is generally considered to be secure, users can further enhance their device’s security by installing reputable security software from trusted developers. These apps can provide additional layers of protection against malware, spyware, and other security threats.
By following these precautions and best practices, iPhone users can significantly reduce the risk of falling victim to a mercenary spyware attack and protect their personal data and privacy. Additionally, staying informed about emerging threats and security vulnerabilities can help users adapt their security practices to evolving threats in the digital landscape.
